WHY THIS MATTERS IN BRIEF
Researchers have used sound to break the worlds’ toughest encryption standard.
Security researchers have successfully broken one of the most secure encryption algorithms, 4096-bit RSA, by listening — yes, with a microphone — to a computer as it decrypts some encrypted data. The attack is fairly simple and can be carried out with rudimentary hardware. While the repercussions for the average computer user are minimal, but if you’re a secret agent, power user, or some other kind of encryption using miscreant, you may want to reach for the Rammstein when decrypting your data.
This acoustic cryptanalysis carried out by Daniel Genkin, Adi Shamir (who co-invented RSA) and Eran Tromer uses what’s known as a side channel attack. A side channel is an attack vector that is non-direct and unconventional and, consequently, hasn’t been properly secured. For example, your password prevents me from directly attacking your phone but if I could work out your pass code by looking at the greasy fingerprints on your screen that would be a side channel attack. In this case, the security researchers listen to the high-pitched (10 to 150 KHz) sounds produced by your computer as it decrypts data.
This might sound crazy but with the right hardware it’s actually not that hard. For a start, if you know exactly what frequency to listen out for you can use low and high pass filters to ensure that you only have the sounds that emanate from your PC while the CPU decrypts data and, in case you were wondering, the acoustic signal is actually generated by the CPU’s voltage regulator as it tries to maintain a constant voltage during wildly varied and bursty loads. Then, once you have the signal, it’s time for the hard bit – actually making sense of it.
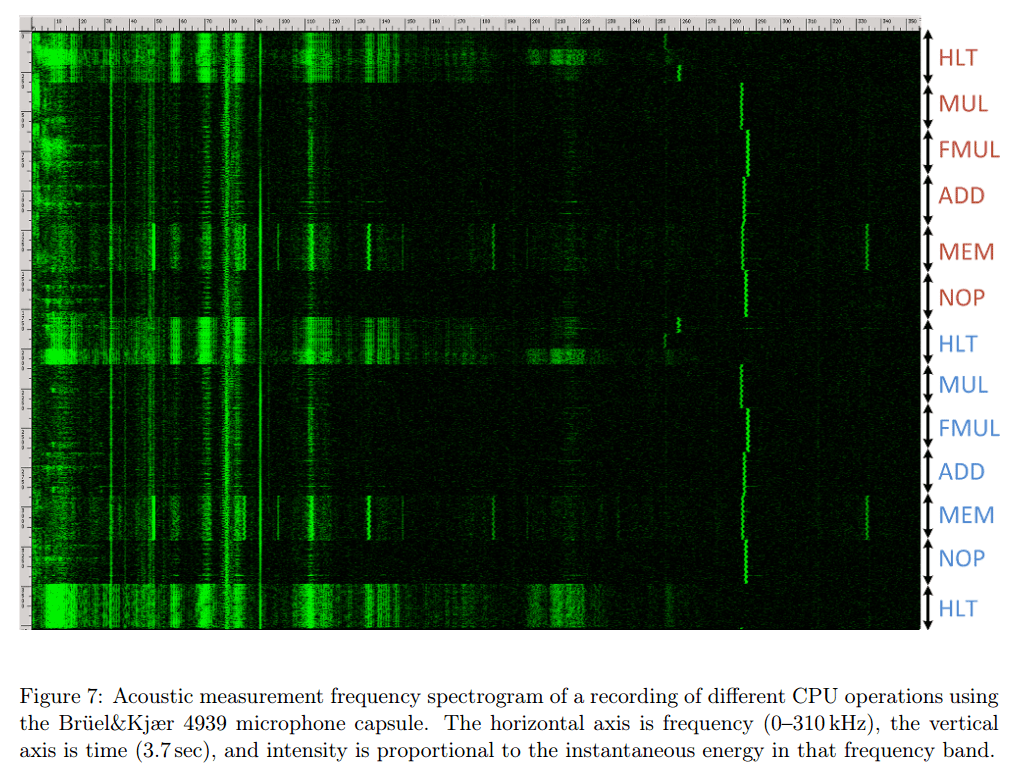
Here you can see the frequency spectrogram of various CPU instructions down the right hand side.
Without going into too much detail, the researchers focused on a very specific encryption implementation – the GnuPG, an open and free version of PGP, 1.x implementation of the RSA cryptosystem. With some very clever cryptanalysis, the researchers were able to listen for telltale signs that the CPU was decrypting some data and then listening to the following stream of sounds to divine the decryption key. The same attack would not work on different cryptosystems or different encryption software, for that they’d have to start back at the beginning and work out all of the tell tale sounds from scratch again.
The researchers successfully extracted decryption keys over a distance of four meters with a high quality parabolic microphone. Perhaps more intriguingly, though, they also managed to pull of this attack with a smartphone placed 30 centimeters away from the target laptop. The researchers performed the attack on different laptops and desktops, with varying levels of success. For what it’s worth, the same kind of electrical data can also be divined from many other sources — the power socket on the wall, the remote end of an Ethernet cable, or merely by touching the computer (while measuring your body’s potential relative to the room’s ground potential).
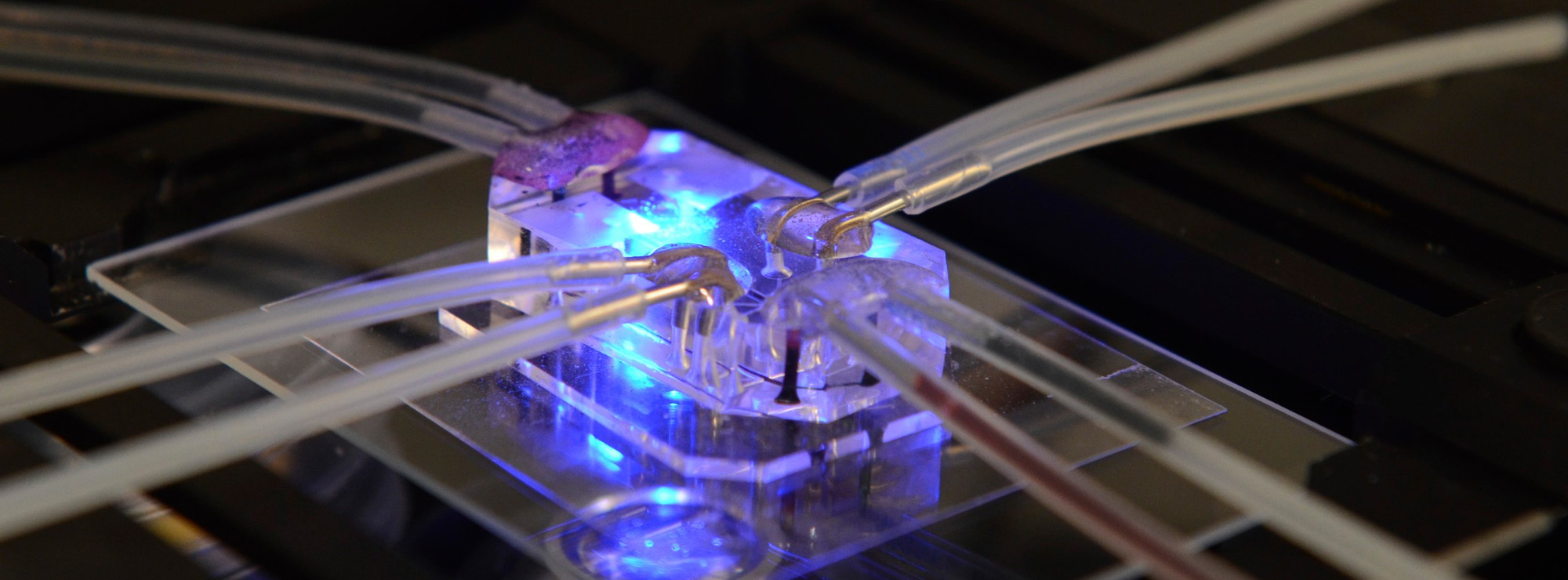
In this light-weight setup, only the microphone (B) needs to be positioned correctly, everything else could be hidden away.
In terms of real world repercussions, acoustic cryptanalysis is actually surprisingly dangerous. Imagine if you were decrypting some files in a library, coffee shop, or other public space someone could obtain your decryption key just by placing their phone near your computer. Alternatively, an attacker could use spear phishing to put malware on your phone that listens for the decryption key. With HTML5 and Flash able to access the microphone it would be possible to build a website that listens for encryption keys too. The researchers propose one particularly nefarious scenario: Put a microphone into a co-located server, slot it into a rack in a data center and then scoop up the encryption keys from hundreds of nearby servers.
If you want to keep your data secure, you only really have two viable options: Heavy-duty encryption, physical security, and ideally both at the same time. If an attacker can’t get physically close to your data, it instantly becomes much harder to steal it. As far as mitigating acoustic cryptanalysis attacks, you either implement physical security keep your laptop in a sound tight box or never let anyone near your computer when you’re decrypting data, alternatively use a strong wide band noise source to cover it up, something like Taylor Swift should probably do it.