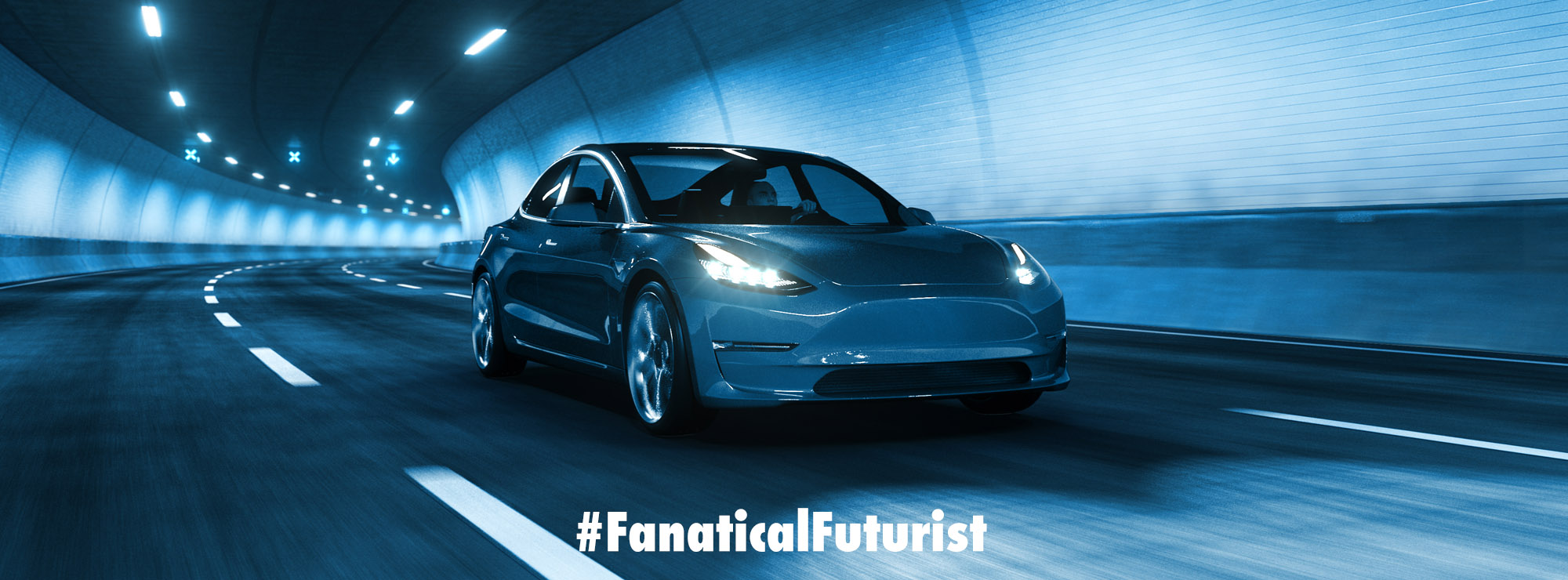
Tesla has now fixed the exploit but this isn’t the first time, or the last time that hackers will take control of individual cars, or entire fleets of autonomous vehicles, and that raises concerns
It’s not the first time that we’ve heard this kind of news and it certainly won’t be the last but a team of researchers from China’s Keen Security Lab, a division of Chinese internet behemoth Tencent, were able to remotely hack into a Tesla Model S by exploiting the vehicle’s in car web browser. While the Keen group worked closely with Tesla’s own security team to fix the vulnerability before it could be put to any nefarious use, the hackers showed it was possible to control many functions of Tesla’s flagship sedan, including the brakes and the sunroof from miles away.
By connecting the car to a malicious WiFi hotspot, the Keen team was able to access the vehicle’s control systems through the CAN bus via the web browser and the team showed off their hack in a video. They were able to remotely search for a destination on the car’s GPS, control the entertainment and instrument screens, pop the trunk and even hit the brakes while the vehicle was in motion twelve miles away and a little less harrowing for the occupants they were also able to adjust the seats and open the sunroof from afar.
The conditions for the exploit though were fairly specific, but it’s not hard to see the danger it would have presented if the team had been a group of malicious hackers and thankfully Tesla patched the exploit within 10 days of receiving the notification of the hack.
“The issue demonstrated is only triggered when the web browser is used, and also required the car to be physically near to and connected to a malicious wifi hotspot,” Tesla said in a statement.
“Our realistic estimate is that the risk to our customers was very low, but this did not stop us from responding quickly.”
While the Keen Security Lab team is withholding additional details on the hack it’s important to note that this is not something current owners should be worried about at this point. As is common practice in White Hat hacking circles, security exploits like this are generally not discussed publicly until they are patched or the exploited company has a chance to respond.
For their part, Keen praised Tesla’s “proactive attitude” while Tesla’s own statement went on to say,
“We engage with the security research community to test the security of our products so that we can fix potential vulnerabilities before they result in issues for our customers. We commend the research team behind today’s demonstration and plan to reward them under our bug bounty program, which was set up to encourage this type of research.”
As the world becomes increasingly connected there are many more questions about security than answers though but slowly we are seeing the emergence of new ways and techniques to try to combat these kind of exploits such as DARPA’s Artificial Intelligence Robo-hackers that find vulnerabilities in systems and patch them automatically and Tor’s Dark Web obfuscation technology which makes it impossible to find targets in the first place.
That said though, there is a long, long way to go and it’s unlikely that any of us, or anything, will ever be truly “secure”.