WHY THIS MATTERS IN BRIEF
If your storage system can detect anomalous ransomware behaviour before your files get encrypted then it can stop it and save your company.
 Love the Exponential Future? Join our XPotential Community, future proof yourself with courses from XPotential University, read about exponential tech and trends, connect, watch a keynote, or browse my blog.
Love the Exponential Future? Join our XPotential Community, future proof yourself with courses from XPotential University, read about exponential tech and trends, connect, watch a keynote, or browse my blog.
In an attempt to beat Ransomware before it spreads through a company’s precious systems IBM has introduced Artificial Intelligence (AI) enhanced capabilities within its new storage solutions to bolster data resilience against ransomware and other cyber threats. Given the persistent and escalating risks posed by cyberattacks, IBM’s enhancements come at a critical time.
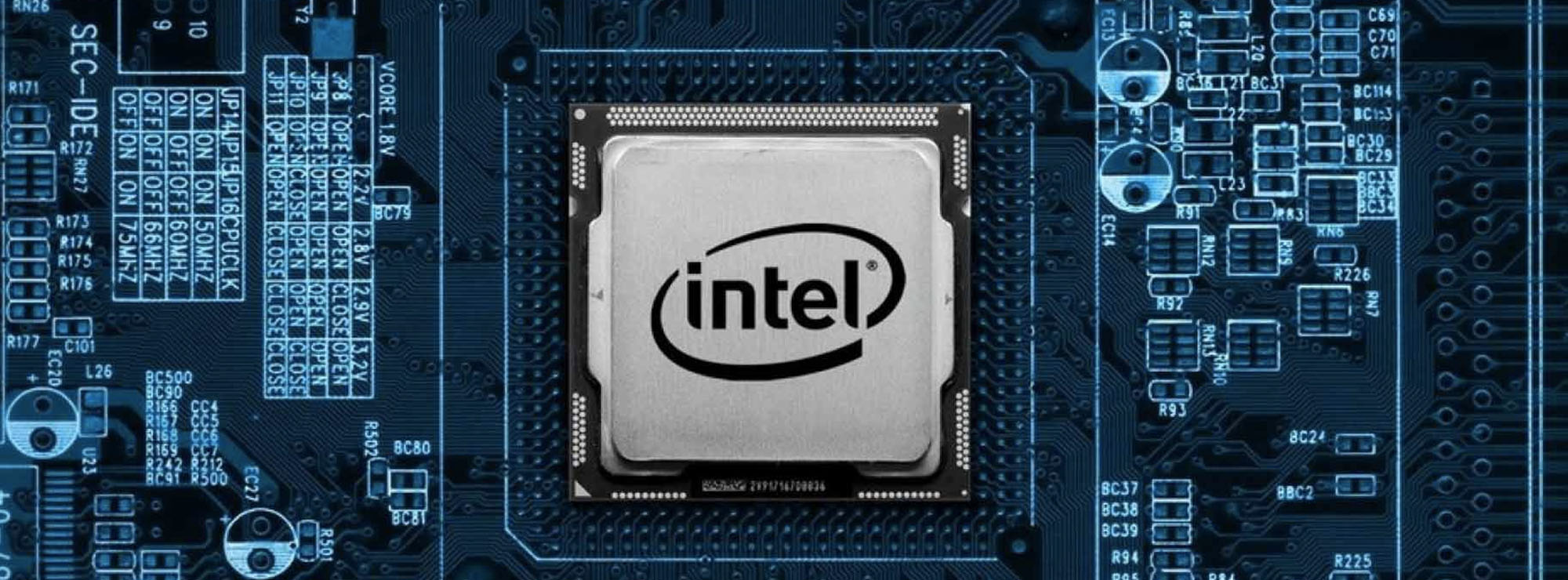
The new cyber-protection capabilities center around IBM’s fourth generation FlashCore Module technology that, working in concert with a freshly updated IBM Storage Defender release, aims to improve threat detection and response by detecting anomalies directly in the data path.
To understand how all this works, you want to talk to the CTO for IBM Flash Storage, and IBM Fellow, Andy Walls. It’s his job to lay out the technical vision for IBM’s storage products, including the novel use of its FlashCore Module technology to solve challenging problems as close to the data as possible.
Thankfully, once a year, like Punxsutawney Phil on Groundhog Day, IBM releases Andy from what I like to imagine is a basement lab crammed with old RK07 disk packs scattered amid petri dishes of DNA storage prototypes so that he can tell the world about IBM’s latest advancements in storage technology.
This time around, Andy picked up right where he left off at the end of his last conversation, nearly a year ago, where he first described how IBM planned to use the computational storage capabilities of its FlashCore module to detect ransomware by looking at the entropy of data as it’s written to flash memory.
Andy describes FlashCore as a computational storage device. This means that a FlashCore Module combines NAND flash for persistent storage, RAM for caching, and a compelling amount of on-device compute to deliver greater functionality than a traditional SSD could.
The FCM takes some of the array’s computationally heavy work, such as compression, from the storage controllers and performs that work directly on the drive. This leads to a variety of efficiencies. It’s also where the IBM FlashSystem now looks for data anomalies that might indicate the presence of ransomware.
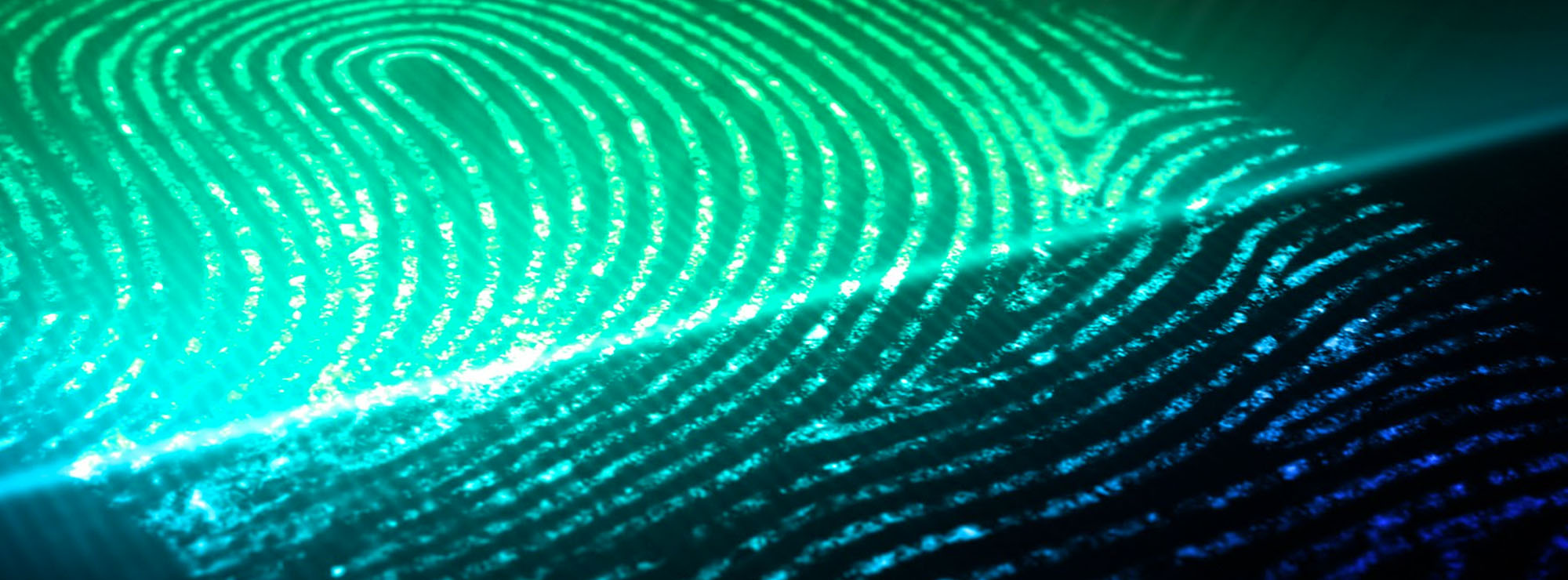
IBM’s new ransomware detection capabilities enable real-time data monitoring at the I/O level, using machine learning models to detect anomalies indicative of ransomware in under a minute.
IBM FlashSystem products scan all incoming data with block-level granularity as it’s written. This process involves inline data corruption detection software and cloud-based AI to identify anomalies that might signal the onset of a cyber-attack, including ransomware. This early detection mechanism allows for immediate response actions to mitigate the attack.
The fourth generation FCM technology enables AI capabilities within the IBM Storage FlashSystem family. Using machine learning models, it continuously monitors statistics gathered from every I/O operation.
IBM trained these models to detect anomalies that resemble ransomware behavior. IBM’s Zurich-based research team is helping maintain a database of ransomware I/O signatures that will keep the system current with the evolving threat landscape.
The FCM captures and summarizes detailed statistics about every I/O in real-time. Leveraging machine learning models, the system can distinguish between normal behavior and patterns indicative of ransomware or malware, allowing immediate corrective actions to protect the data.
The IBM FlashSystem analyzes parameters such as the data’s compressibility and randomness – its entropy. This information is passed to IBM Storage Insights software, which can alert operators when a workload anomaly is detected. For instance, if ransomware begins to encrypt an application’s data, the system can detect this unusual behavior based on the change in data characteristics.
Central to IBM’s overall data protection capabilities is its upgraded IBM Storage Defender software. The new release uses AI-powered sensors to integrate FlashSystem detection with broader threat detection capabilities across various IT environments, including VMs, databases, applications, and containers.
The new version also introduces workload and storage inventory management features to aid organizations in incorporating their assets into a business continuity plan for post-attack recovery. Integration with other IBM Storage and Security solutions and third-party data platforms provides end-to-end data resilience.
Key innovations include the ability for storage administrators to create protection groups for automatic backup and to restore or recover immutable data copies free from threat signatures to multiple locations. IBM has also integrated settings for creating Safeguarded Copy snapshots, which are cyber-resilient and isolated from production data, enabling quicker recovery after data loss events.
IBM’s sophisticated approach enables its storage solutions to provide early warnings of cyber threats, allowing enterprises to recover faster and maintain the confidentiality and security of their data against ransomware and other cyber-attacks.
Data protection and cyber-resiliency features are quickly becoming standard offerings within enterprise storage solutions. Immutable snapshots, for example, are now part of solutions from nearly every top-tier storage vendor. Scanning snapshots using entropy calculations like those used by IBM for anomalies is also becoming popular.
The challenge with the approaches taken by most storage solutions is that detection often happens after the fact. Once a snapshot is found to be corrupt, it may be too late. You have to work backward in time to find good data to restore.
IBM’s approach closes that gap, alerting the user nearly instantly when an anomaly is detected. This happens long before the corrupted data is written to a snapshot. That’s precisely the kind of protection you want in your enterprise.
IBM isn’t the only storage provider building this level of real-time anomaly detection directly into its storage arrays. NetApp’s Autonomous Ransomware Detection feature in its ONTAP products also looks at entropy to detect anomalies and raise alerts.
Unlike IBM, NetApp performs the computation on its storage controllers, not within the underlying drives. NetApp’s approach also doesn’t detect ransomware using signatures; instead, it relies on entropy, file extensions, and the amount of file write activity. IBM is currently alone in delivering this level of storage-based threat detection.
While most of the storage industry spends R&D budget coaxing enterprise-class storage out of commodity server-class hardware, IBM is one of only a small handful of technology providers continuing to innovate storage with a full-stack view of the platform.
IBM’s storage solutions remain among the most technologically advanced on the market, making them ideal to protect critical enterprise data. The new ransomware detection features only solidify that position.