WHY THIS MATTERS IN BRIEF
As more organisations are subjected to cyber attacks it is important they have a way to evaluate their readiness, and their ability to identify, mitigate and manage events.
It was a big day for IBM on Monday as it opened its new security headquarters in Kendall Square in Cambridge, MA, complete with what the company is calling the first commercial “Cyber Range,” and with national agencies such as GCHQ proposing radical solutions to prevent cyber crime that include building national firewalls IBM’s timing seems to be on point.
Cyber ranges are network security testing environments and they’re typically only run by the military, government agencies – think GCHQ again, and the NSA – or military contractors, such as Raytheon. This one, dubbed X-Force Command, however, is much more than a couple of terminals in a lab. It is a massive setup with seats for 36 operators. It features audio, video and a simulated Fortune 500 company operation with the goal of giving the user a realistically simulated cyber crisis.
It includes nearly a petabyte of data running in a data center underneath the cyber range and includes all the kinds of operations that you would have running in a typical enterprise, such as E-Mail servers, supply chain software, employees using the internet and everything else – including the kitchen sink.
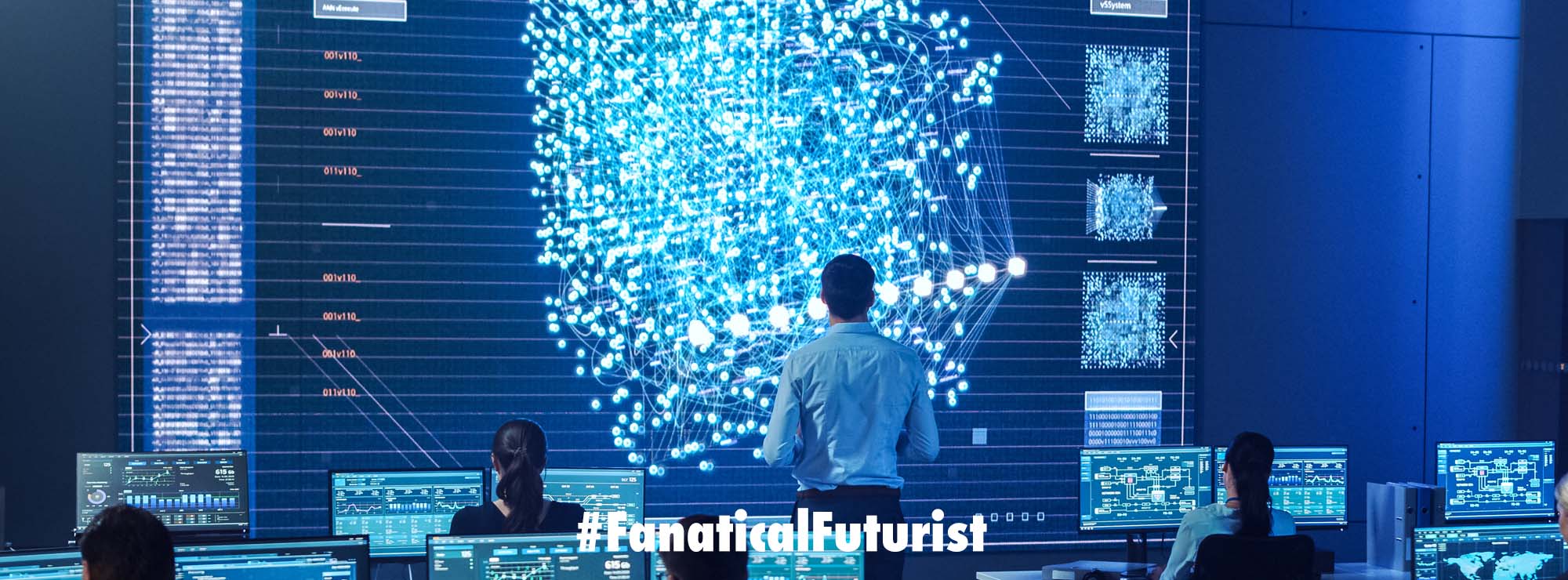
The idea behind the cyber range is to use it to simulate a wide variety of cyber attacks and events to show security personnel, C-suite executives or anyone just how prepared, or as is more likely, how unprepared they are to deal with a massive breach.
It’s cyber attack roleplay for adults.
“We are putting you into a simulator that is so realistic that your pulse will race, and you will be stressed, and you will learn how to make critical decisions in a crisis,” Caleb Barlow, vice president of security at IBM explained.
The cyber range is part of a broader security strategy by the company. Over the last couple of years, it has purchased at least seven other security companies, including Resilient Systems earlier this year, which helps companies prepare for a cyber attack before they happen.
While the range isn’t specifically a sales tool its main purpose, says Barlow, is to use is as an education and awareness-raising tool. It’s designed to show people in stark terms what happens during a breach, and how they might react during and after an incident – especially if they are unprepared.
The simulations the center can run are all designed to help organisations understand the different aspects of breach response which include everything from identifying that a breach has occurred in the first place all the way through to how to report the incidents to the regulators and government officials and how to deal with the press.
Hopefully, if the organisations have thought this through beforehand then they should have a playbook and this center aims to put that playbook to the flames and test it to its core and IBM wouldn’t be IBM without a consulting piece, so naturally they have built a team of consultants to help customers prepare for an attack and deal with the aftermath.