
Someone is probing the critical infrastructure of the internet for weaknesses and the attacks are getting larger
Many people think the internet is persistent with multiple points of failure but it, like many other systems relies on a number of key, critical components to keep it running and now those seem as though they are under attack. Unknown to many over the past year or two, someone has been probing the defenses of the companies that run critical pieces of the Internet. These probes take the form of precisely calibrated attacks designed to determine exactly how well these companies can defend themselves, and what would be required to take them down. We don’t know who is doing this, but it feels like a large nation state. China or Russia would be most people’s first guesses.
First, a little background.
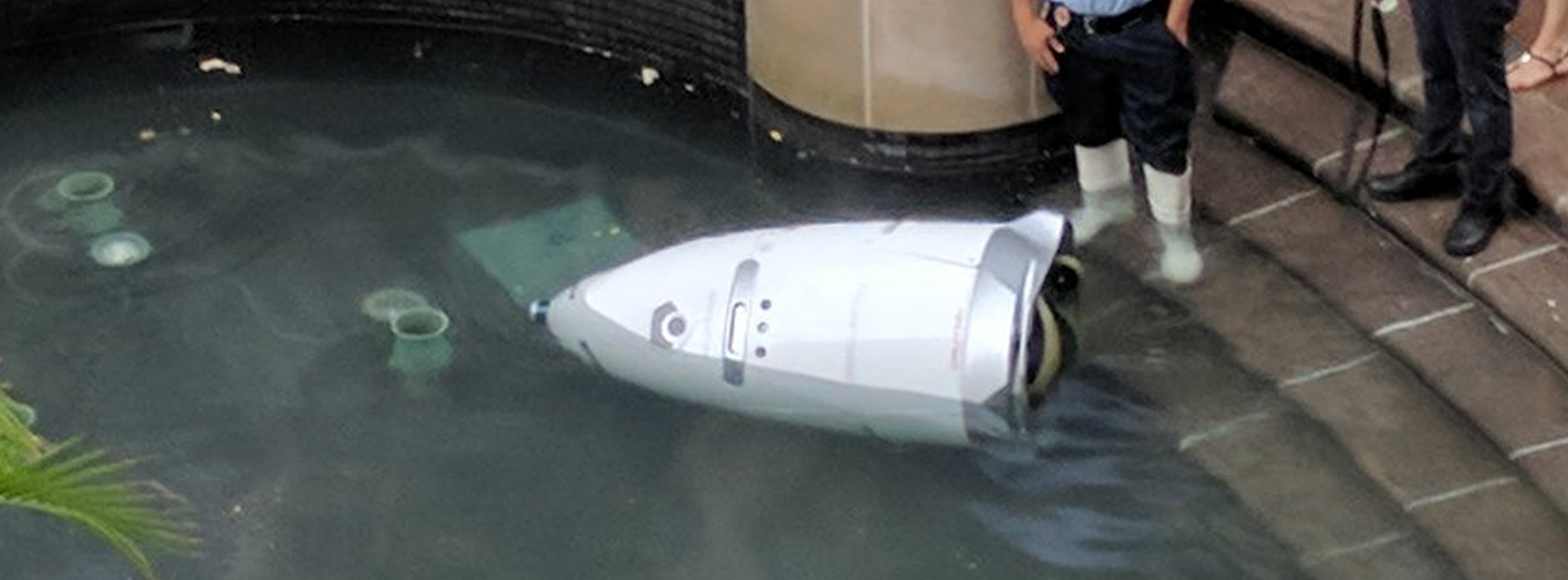
If you want to take a network off the Internet, the easiest way to do it is with a Distributed Denial-of-Service attack (DDoS). Like the name says, this is an attack designed to prevent legitimate users from getting to the site. There are subtleties, but basically it means blasting so much data at the site that it’s overwhelmed. These attacks are not new – hackers do this to sites they don’t like, and criminals have done it as a method of extortion. There is an entire industry, with an arsenal of technologies, devoted to DDoS defense but largely it’s a matter of bandwidth. If the attacker has a bigger fire hose of data than the defender has, the attacker wins.
Recently, some of the major companies that provide the basic infrastructure that makes the Internet work have seen an increase in DDoS attacks against them. Moreover, they have seen a certain profile of attacks. These attacks are significantly larger than the ones they’re used to seeing. They last longer. They’re more sophisticated. And they look like probing. One week, the attack would start at a particular level of attack and slowly ramp up before stopping. The next week, it would start at that higher point and continue. And so on, along those lines, as if the attacker were looking for the exact point of failure.
The attacks are also configured in such a way as to see what the company’s total defenses are. There are many different ways to launch a DDoS attack. The more attack vectors you employ simultaneously, the more different defenses the defender has to counter with. These companies are seeing more attacks using three or four different vectors. This means that the companies have to use everything they’ve got to defend themselves. They can’t hold anything back. They’re forced to demonstrate their defense capabilities for the attacker.
While the sources are unable to give precise details of the attacks because of the security implications this all is consistent with what Verisign is reporting. Verisign is the registrar for many popular top-level Internet domains, like .com and .net and if it goes down then there would be a global blackout of all websites and E-Mail addresses in the most common top level domains.
Every quarter, Verisign publishes a DDoS trends report. While its publication doesn’t provide details the trends and patterns we’re seeing reported from critical infrastructure providers around the world are the same: “In Q2 2016, DDoS attacks continued to become more frequent, persistent, and complex.”
One company, who spoke on condition of anonymity, told reporters about a variety of probing attacks in addition to the DDoS attacks – testing the ability to manipulate Internet addresses and routes, seeing how long it takes the defenders to respond, and so on.
Someone is extensively testing the core defensive capabilities of the companies that provide critical Internet services.
Who would do this? It doesn’t seem like something an activist, criminal, or researcher would do. Profiling core infrastructure is common practice in espionage and intelligence gathering. It’s not normal for companies to do that. Furthermore, the size and scale of these probes – and especially their persistence, points to state actors. It feels like a nation’s military cybercommand trying to calibrate its weaponry in the case of cyberwar.
So what can companies do about this? Nothing really it seems – noone knows where the attacks are coming from but some data is suggesting China but then again it’s possible to disguise the country of origin for these sorts of attacks. The NSA, which has more surveillance in the Internet backbone than everyone else combined, probably has a better idea, but unless the US decides to make an international incident over this, or a public comment, we won’t see any attribution.







The very wealthy have a love-hate relationship with the internet. They love all the wealth it creates for them, hate the power it’s taken from them and given to the common man. They study real history. They know that the invention that deposed the ancient monarchies, feudal lords and religious authorities was the printing press, which in a sense was the first internet because it allowed ideas to flourish, increased literacy and education. What followed was a revolution of the merchant class over the ancient and backward systems of government. The internet is like the printing press on steroids, and now these holders of ancient power and wealth find themselves in the same obsolete position as those their ancestors stole power from centuries ago. The writing is on the wall, and they will do anything to postpone the inevitable including trying to pull the plug. In the end, evil always destroys itself.