WHY THIS MATTERS IN BRIEF
There are many ways people can spy on you, and now they can listen in on your conversations by monitoring your hard drives vibrations.
Everything can be hacked in order to spy on “stuff” it seems, whether it’s hacking ultra secure air gapped systems, like the ones used in top secret datacenters, or even “unhackable” quantum encryption, and now even the humble hard drive it turns out can be used to spy on your private conversations after researchers from the University of Michigan Zhejiang in China demonstrated that they can be turned into highly effective evesdropping devices.
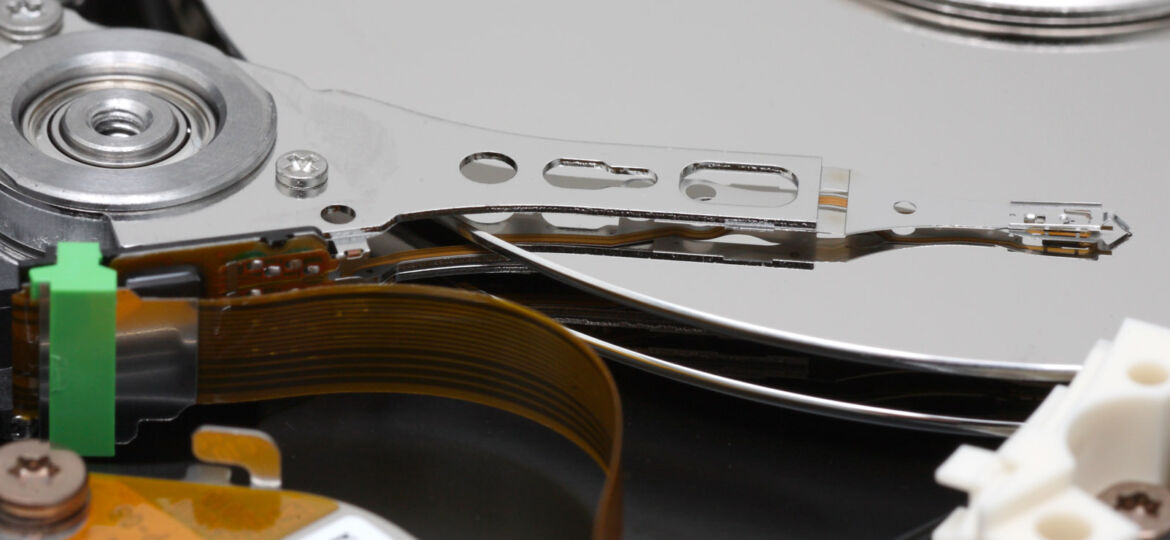
Turning a hard drive into a listening device doesn’t have anything to do with its data storage capabilities though. Instead, the team leveraged the sensors that help control the position of the read head above the platters. The head needs to be in precisely the right spot on the track to operate — even a few nanometers can be the difference between perfect functionality and a corrupted file. The drive’s internal sensors generate what’s called a Positional Error Signal (PES), and this is how the researchers extracted sounds from the hard drive.
Any vibration can alter the position of a hard drive, so a modern hard drive is sensitive enough to pick up even minute disturbances in the platter. And yes, even human speech shows up in the PES data, but of course, hard drives don’t broadcast PES readings for everyone to analyse.
In a proof of concept experiment, the team installed modified firmware on the drives that could record the PES measurements. Using that data, the researchers created high-quality recordings of human voices, and in another test the PES data was sufficient to reconstruct music playing near the hard drive. It was so accurate that the music ID app Shazam was able to identify the song.
There are a few notable drawbacks to this eavesdropping method though. For one, you need physical access to the hard drive to implant the malicious firmware. Then, you need a package on the computer with internet access to send the PES data. It’s not impossible – state actors have been known to intercept computers and implant bugs before sending them along to the target. The other issue is the sounds near the hard drive need to be rather loud. For human speech, you’re looking at 75dB minimum, which is like having an almost-argument within a few feet of a hard drive, and to ID music it needs to be playing at about 90dB which is the same volume as a lawnmower.
So, the result is that for now your hard drive probably isn’t spying on you, but if you’re an attractive enough target, then, well, who knows, and as the exploit gets fine tuned one day it’ll inevitably be able to detect even a whisper… so be careful what you say.