WHY THIS MATTERS IN BRIEF
As the volume and variety of global cyber attacks increase exponentially this is a wake up call that we need a new way to defend ourselves.
The US military’s cybersecurity capabilities aren’t advancing fast enough to stay ahead of the “onslaught of multipronged” attacks envisioned by adversaries, the Pentagon’s combat testing office has warned. And if they can’t keep up then there’s Bob Hope and no hope for the rest of us, and. personally I think it’s high time we consider new approaches to tackle the inevitable onslaught that’s coming as we now start to face the prospect of self-evolving, self-replicating Artificial Intelligence (AI) Robo-Hackers that can operate and spread millions of times faster than attacks created and propagated by human hackers – and that’s just one of a myriad of game changing cyber threats we’re facing.
Despite some progress in fending off attacks staged by in-house “Red Teams,” the testing office said “we estimate that the rate of these improvements is not outpacing the growing capabilities of potential adversaries who continue to find new vulnerabilities and techniques to counter fixes.”
Automation and AI are beginning to “make profound changes to the cyber domain,” a threat that the military hasn’t yet fully grasped how to counter, Robert Behler, the Defense Department’s director of operational test and evaluation, said in his annual assessment of cyber threats, which was obtained by Bloomberg News recently.
The test office’s findings may be discussed on Tuesday during a Senate Armed Services hearing focused on Pentagon cyber policy with Chief Information Officer Dana Deasy.
The evaluation, part of the testing office’s annual report that may be released as early as this week, comes amid other critical appraisals of the military’s ability to maintain and improves its defense against computer attacks.
In an acknowledgment of potential threat from AI, the US Army says it is seeking information about “Autonomous Cyber” capabilities, or Robo-Hackers to you and I, like the one called “Mayhem” that the Pentagon just strapped into its critical systems, that would use AI and machine learning to automatically and autonomously defend its networks and protect its own intelligent systems against sophisticated cyberattacks. In other words, the Army wants to pit AI against AI in cyberspace. And yes that is as fun and as scary as it sounds – let’s just hope it all ends well. Ha.
In October, the Government Accountability Office issued a withering assessment, saying the US military had failed to make cybersecurity for its multibillion-dollar weapons systems a major focus until recently, despite years of warnings.
“We have not reviewed the latest report” from Behler “but DOD faces significant challenges in securing its weapon systems from cyber threats,” said Cristina Chaplain, the GAO director who managed the agency’s report, adding, “DOD testers routinely found mission-critical vulnerabilities in systems under development, and in some cases, repeatedly over the years,” and program officials “tended to discount the scale and severity of the problem.”
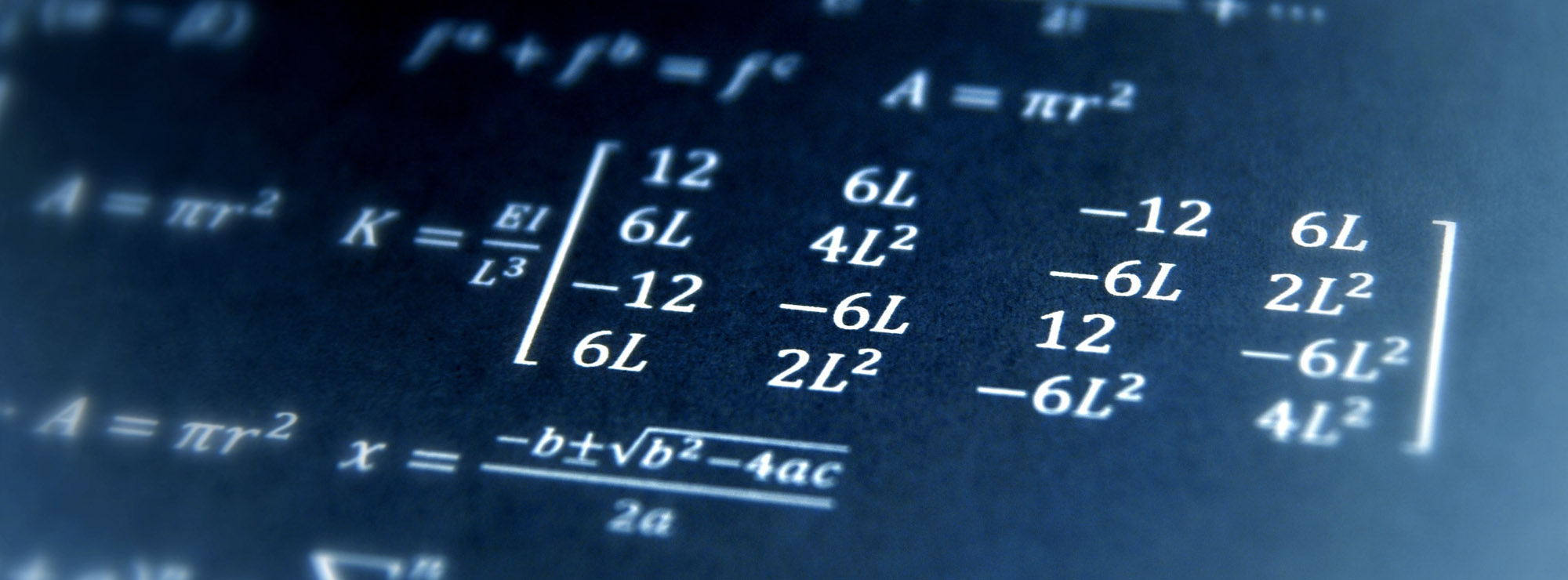
Behler’s report also reinforces those concerns, saying the Pentagon’s cyber testing is “handicapped by lack of expertise and tools to assess software-intensive weapons systems.”
The highlights of the report included the fact that the ground control network for the US Air Force’s new GPS III satellites was “in need of cybersecurity hardening,” that Lockheed Martin’s “flying computer” the F-35 and its 8 million lines of code “showed that some of the vulnerabilities identified during earlier testing periods still had not been remedied,” and that the new Department of Veterans Affairs health care records management system known as Genesis “would not survive in a cyber-contested environment.”
Analysing four years of after-action reports on cyber exercises, Behler’s office report also. found “defenders demonstrated increasing ability to detect Red Team activity.” But it also said “defenders need to improve speed and accuracy for processing reported incidents.”
Red Teams operated by the Army’s Threat Systems Management Office conducted more than 200 penetration events in 2018. While the mock attackers succeeded in many cases, there were “a growing number of instances where Red Teams needed more time” to achieve their objectives partly thanks to “improved network defenses,” the testing office said.
Behler also warned of a crisis in recruiting and retaining qualified Red Team commandos, who attempt damaging penetrations of networks and weapons systems using the tactics of adversaries such as Russia, China, North Korea or Iran.
Most Pentagon cybersecurity jobs “are not compensated commensurate with the position’s required time and expertise,” increasing the risk of losing trained personnel to higher-paying private work, according to the report.
Behler then suggested the Pentagon should provide seed funding for a select group of military service academies, private companies, universities and national laboratories “to grow the DoD’s cybersecurity testing workforce and capabilities” while developing automated tools because “hiring more cyber experts will not be enough.”