WHY THIS MATTERS IN BRIEF
Artificial Intelligence is a cyber security game changer, for better and worse, and we need to be better prepared for what’s coming.
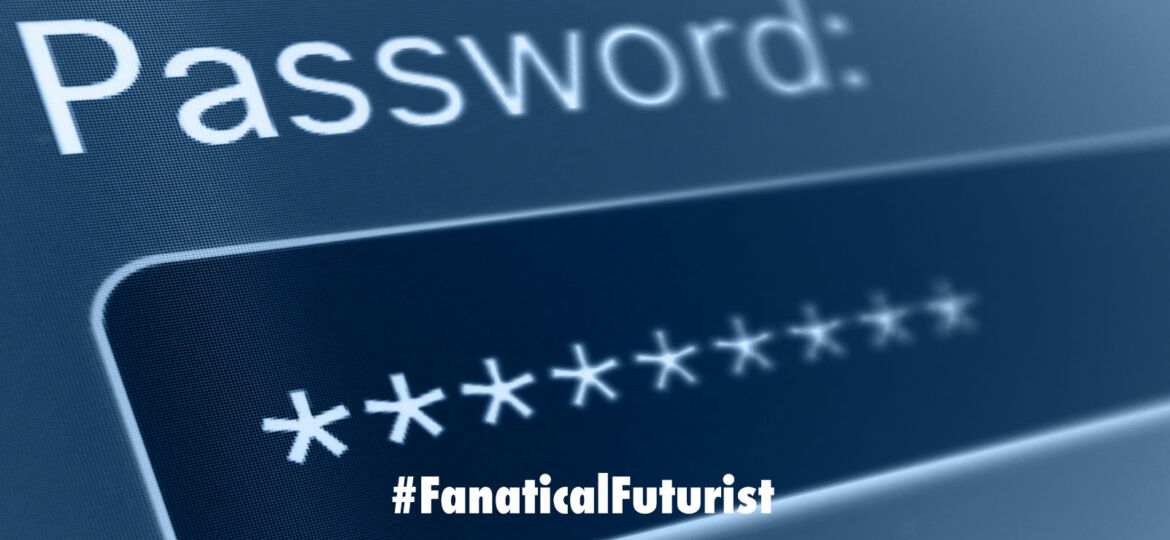
Last year the credit reporting agency Equifax announced that malicious hackers had leaked the personal information of over 143 million people after their system was hacked, and while that’s concerning it’s long been known that if a hacker wants to access your online data by simply guessing your password then there’s a high chance you’ll be toast in less than an hour. Now though after a recent announcement there’s even more bad news for users – scientists at the Stevens Institute of Technology in New Jersey have found a way using Artificial Intelligence (AI) to create a program that, when combined with existing hacker tools, took just minutes to figure out more than a quarter of all the passwords from a set of more than 43 million LinkedIn profiles. And perhaps yours was one of them…? Despite this concerning turn of events though the same researchers say the technology may also be able to be used to beat hackers at their own game by helping users measure the strength of their passwords.
“The new technique could also potentially be used to generate decoy passwords to help detect breaches,” says Thomas Ristenpart, a computer scientist who studies computer security at Cornell Tech in New York who wasn’t involved with the study, which is something that another team accomplished last year by creating a bot that tells you when your accounts have been hacked even when the companies being hacked didn’t know, or didn’t fess up to the fact.
The strongest password guessing programs on the darkweb today, John the Ripper and hashCat, use several techniques to guess and crack people’s passwords. One is simple brute force where they randomly try lots and lots of different combinations of characters until they get the right one, but other approaches involve extrapolating new password guesses by using previously leaked passwords as a reference. By using this latter approach on some sites these programs have managed to guess more than 90 percent of passwords, but in order to achieve this staggeringly high success rate they’ve required many years of manual coding to build up their attacks.
The team at Stevens aimed to speed up this process by turning to deep learning, a brain inspired approach at the cutting edge of AI. The researchers started with a so called Generative Adversarial Network, or GAN, the same type of AI behind the amazing new wave of creative and innovative machines, that’s made up from to different artificial neural networks, for example, a “Generator network” attempts to produce artificial outputs, such as images, that resemble real examples of actual photos, while a “Discriminator network” tries to detect the real ones from the fakes.
The two networks help refine each other until the generator, quite literally, becomes a skilled counterfeiter, such as the one from Nvidia which produced life like photos of “fake” celebrities that people can’t tell apart from the real thing, but while these GANs have been used to make realistic images, as well as fake news content, their skills haven’t been applied much to text.
The researchers created a GAN called PassGAN and then compared it with two versions of hashCat and one version of John the Ripper. The team then fed each tool tens of millions of leaked passwords from a gaming site called RockYou, and asked them to generate hundreds of millions of new passwords on their own. Then they counted how many of these new passwords matched a set of leaked passwords from LinkedIn as a measure of how successful they’d be at cracking them.
Initially on its own PassGAN generated 12 percent of the passwords in the LinkedIn set, whereas its competitors generated between 6 percent and 23 percent. But the best performance came from combining PassGAN and hashCat. Together they were able to crack 27% of passwords in the LinkedIn set, and even failed passwords from PassGAN seemed pretty realistic including saddracula, santazone, coolarse18.
“Using GANs to help guess passwords is novel,” says Martin Arjovsky, a computer scientist who studies the technology at New York University who was also involved in the project, before adding that “the paper confirms that there are clear, important problems where applying simple machine learning solutions can bring a crucial advantage.”
Still, Ristenpart says, “It’s unclear to me if one needs the heavy machinery of GANs to achieve such gains. Perhaps even simpler machine learning techniques could have assisted hashCat just as much,” and Arjovsky concurs.
Indeed, an efficient neural net produced by Carnegie Mellon University also recently showed promise, and Ateniese plans to compare it directly with PassGAN before submitting his paper for final peer review.
Ateniese says that though in this pilot demonstration PassGAN gave hashCat an assist, he’s “certain that future iterations could surpass hashCat.” That’s in part because hashCat uses fixed rules and was unable to produce more than 650 million passwords on its own. PassGan meanwhile, which invents its own rules, can create passwords indefinitely.
“It’s generating millions of passwords as we speak,” he says. Ateniese also says PassGAN will improve with more layers in the neural networks and training on many more leaked passwords. He compares PassGAN to AlphaGo, the Google DeepMind program that recently beat a human champion at the board game Go using deep learning algorithms.
“AlphaGo was devising new strategies that experts had never seen before,” Ateniese says. “So I personally believe that if you give enough data to PassGAN, it will be able to come up with rules that humans cannot think about.”
And if you’re worried about your own security, experts have a few suggestions for you such as making them long but still easy to remember, and using two step authentication, but all that said, one thing is for certain, getting hacked may no longer be a matter of if for many people, but when, so just make sure you’re not one of them.